Cloud Computing Security Organisation Assessments Service Categories Responsibility | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

Cloud Computing Conceptabstract Cloud Connection Technology Stock Vector (Royalty Free) 1911593620 | Shutterstock
Beherrschbarkeit Von Cyber Security, Big Data Und Cloud Computing: Buy Beherrschbarkeit Von Cyber Security, Big Data Und Cloud Computing by unknown at Low Price in India | Shopsy.in

Security and Privacy Requirements for Cloud Computing in Healthcare: Elicitation and Prioritization from a Patient Perspective: ACM Transactions on Management Information Systems: Vol 11, No 2

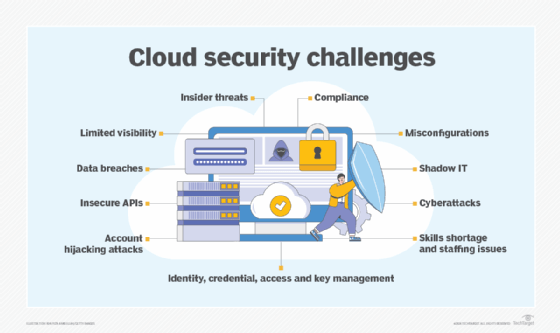
Sicherheit und Cloud Computing: Ratgeber - kritische Funktionen in die Cloud auslagern - TecChannel Workshop

Bestellung Studie: »Cloud Computing Sicherheit – Schutzziele. Taxonomie. Marktübersicht.« - Fraunhofer AISEC