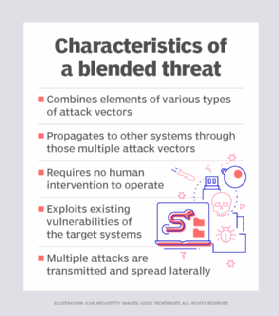
Whiz Security - Blended Threat A blended threat is an exploit that combines elements of multiple types of malware and usually employs multiple attack vectors to increase the severity of damage and

Unistal Global - What is Blended threat? To Protect yourself from any online threat download #ProtegentAntivirus - https://www.protegent360.com/antivirus.html #Protegent is world's only #Antivirus having inbuilt #datarecovery software with advanced ...

Internet Blended Threat Stock Photo - Download Image Now - 2015, Aggression, Antivirus Software - iStock

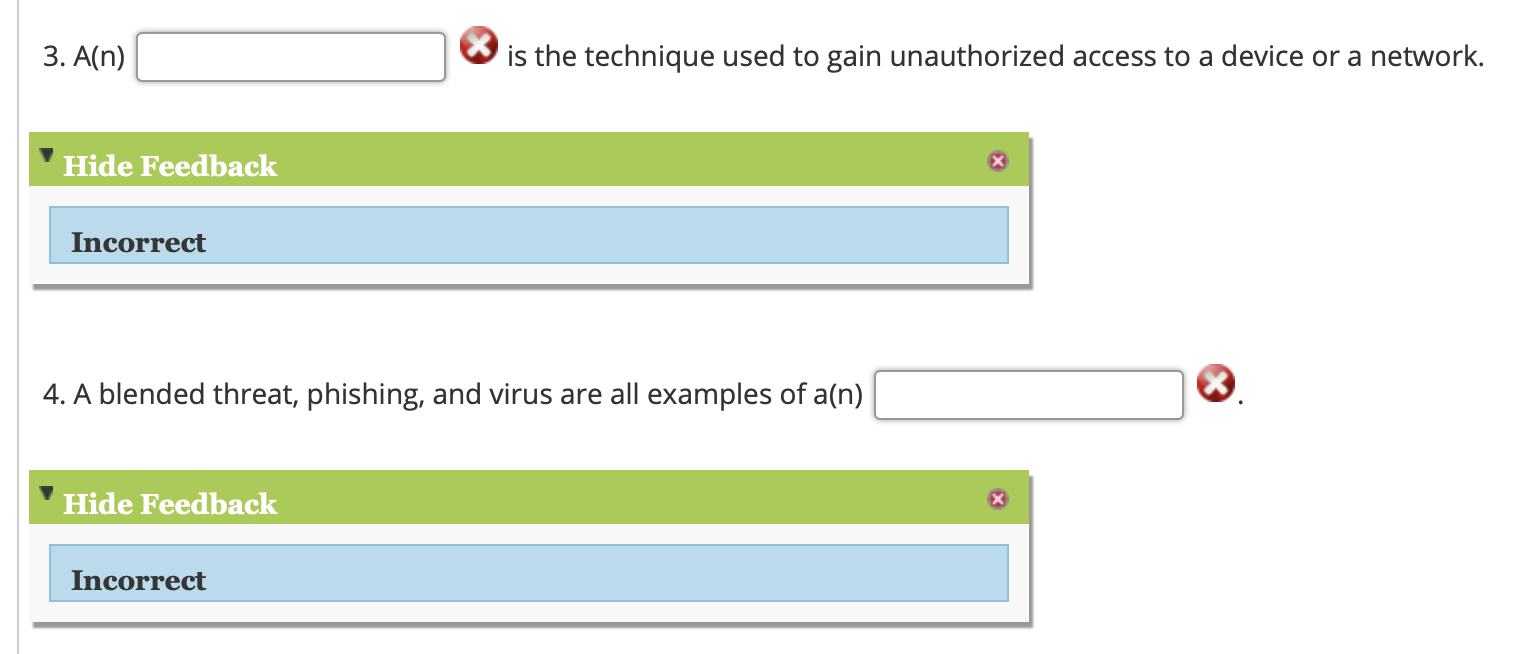
Computer Worm Computer Virus Trojan Horse Malware, PNG, 500x559px, Computer Worm, Artwork, Blended Threat, Computer, Computer
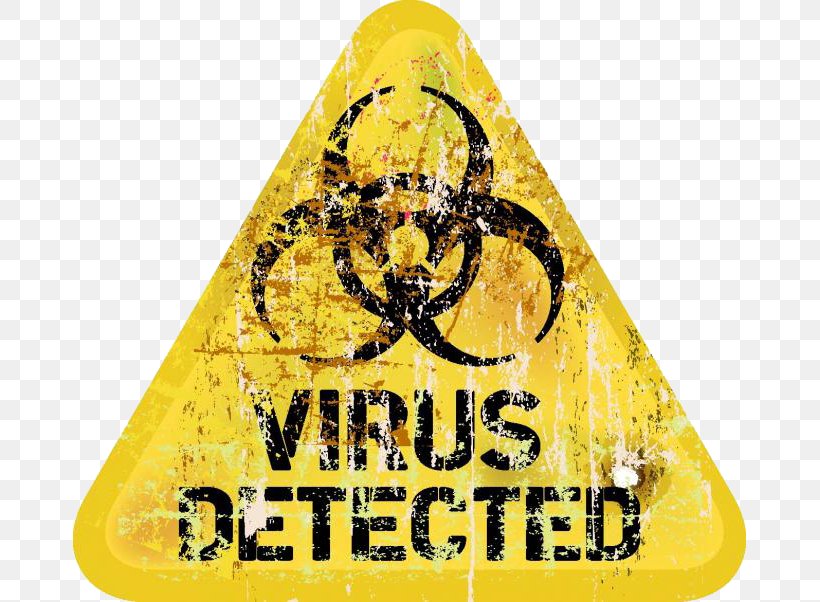


![4. Blended Threats: When Applications Exploit Each Other - Hacking: The Next Generation [Book] 4. Blended Threats: When Applications Exploit Each Other - Hacking: The Next Generation [Book]](https://www.oreilly.com/library/view/hacking-the-next/9780596806309/httpatomoreillycomsourceoreillyimages321278.png)